10 min read

Imagine that you are logged into your website’s admin panel, checking emails and browsing the web as usual. You don’t download any suspicious files or enter your password on a fake website. Yet only a few minutes later, your website’s settings have been altered, new administrator accounts have been created, or requests have been sent that you never intended to make.
It may sound hard to believe, but this is a typical scenario of Cross-Site Request Forgery (CSRF). This type of attack exploits the system’s trust in an already authenticated user, effectively causing the website to “open the door” to hackers without the site owner realizing it. In this article, we will clearly explain what CSRF is, how it works, and why every WordPress website needs to take preventive measures seriously from an early stage.
What is Cross-Site Request Forgery?Link to heading

Cross-Site Request Forgery (CSRF) is a type of attack that forces an end user to carry out unintended actions on a web application where they are already properly authenticated. By using simple social engineering techniques, such as sending a link via email or messaging platforms, attackers can trick users into visiting a page that silently executes requests according to a prearranged attack scenario.
When the victim is a regular user, a successful CSRF attack may cause them to perform actions that change the system’s state, such as transferring money, changing their email address, or modifying account information without their knowledge. More dangerously, if the target is an administrative account, CSRF can go far beyond a single malicious action and potentially expose full control of the system, posing a serious threat to the entire web application.
>>> Learn more: What is a Cross Site Scripting (XSS) attack?
How does Cross-Site Request Forgery work?Link to heading
For a CSRF attack to occur, three critical conditions must be met simultaneously.
- First, the application must contain an action that is valuable to the attacker, meaning an operation that they have a clear incentive to force the user to perform. This action may involve privileged functionality, such as changing other users’ permissions, or any operation related to personal user data, for example updating an account password.
- Second, the application relies entirely on cookie-based session management. The execution of the action is carried out through one or more HTTP requests, and the system uses only the session cookie to identify the user who made the request. There are no additional mechanisms in place to verify the legitimacy of the request or to further validate the session.
- Third, the requests that perform the action do not contain unpredictable parameters. In other words, all parameter values in the request are information that an attacker can either know or easily guess. For instance, a password change function would not be vulnerable to CSRF if the attacker were required to know the user’s current password.

For example, suppose an application provides a feature that allows users to change the email address associated with their account. When a user performs this action, the browser sends an HTTP request similar to the following:
POST /account/update-email HTTP/1.1
Host: example-website.com
Content-Type: application/x-www-form-urlencoded
Content-Length: 34
Cookie: session=ab3F9KxLQm72pEwZtH4cNqP8RsdYxA12
email=user@example.com
This situation satisfies all the necessary conditions for a CSRF attack. Changing the account’s email address is an action of interest to an attacker because once the email has been modified, they can typically initiate a password reset and gain full control over the victim’s account.
The application relies solely on the session cookie to identify the requester and does not implement any additional tokens or mechanisms to track user sessions. Furthermore, the request parameters, specifically the new email address, are values that the attacker can easily determine.
When these conditions are met, the attacker can create a web page containing the following HTML code:
<html><body><form action="https://example-website.com/account/update-email" method="POST"><input type="hidden" name="email" value="attacker@malicious-site.net" /></form><script>document.forms[0].submit();</script></body></html>
If a user visits the attacker’s web page, a sequence of events takes place. First, the page automatically sends an HTTP request to the vulnerable website. If the user is logged in to that website, their browser will automatically attach the session cookie to the request, provided that SameSite cookie restrictions are not configured.
Finally, the vulnerable website processes the request as usual, treats it as a legitimate action performed by the user, and proceeds to change the account’s email address without the user being aware of what has happened.
How dangerous is CSRF for a website?Link to heading

Unauthorized data modificationLink to heading
Cross-Site Request Forgery enables attackers to exploit a user’s valid authenticated session to carry out actions that the website owner never intended. These actions often involve sensitive data, such as changing personal information, editing content, updating system configurations, or submitting critical requests under the user’s identity.
Because the system believes the request originates from a legitimate session, these unauthorized changes are processed normally, leading to data inconsistency and making the root cause difficult to identify in the early stages.
Account takeoverLink to heading
In many cases, CSRF does not stop at altering a single piece of information but becomes a stepping stone toward full account compromise. Attackers may change the email associated with an account, trigger password reset functions, or create additional access privileges.
When the victim is an administrator account, the consequences are far more severe, as the attacker can gain complete control over the website, install malware, create backdoors, or even use the compromised site as a platform to attack other systems.
Legal risks and loss of brand reputationLink to heading
Security incidents caused by Cross-Site Request Forgery not only result in technical damage but also lead to serious legal risks. When user data is altered or exposed, businesses may violate personal data protection regulations, potentially facing complaints, penalties, or legal disputes.
At the same time, brand reputation can be severely affected as customers lose trust in the website’s security, resulting in declining revenue and long-term difficulties in restoring brand image.
How to Prevent Cross-Site Request ForgeryLink to heading

CSRF TokenLink to heading
A CSRF token is a unique, random, and hard-to-guess value generated on the server side and associated with a user’s authenticated session. This token is typically embedded in forms or requests that perform sensitive actions, such as updating account information, changing passwords, or executing transactions.
When a request is submitted, the server verifies whether the CSRF token exists, is valid, and matches the user’s session. If the token is missing or incorrect, the request is immediately rejected. This mechanism ensures that only legitimate actions initiated by the actual user are accepted, making it extremely difficult for attackers to forge requests from external sources.
SameSite CookieLink to heading
SameSite Cookie is a browser-level security mechanism that controls whether a website’s cookies are included in requests originating from other domains. When a session cookie is assigned the SameSite attribute, the browser restricts or completely blocks cookies from being sent in cross-site request scenarios.
This is particularly important for CSRF prevention, as most attacks rely on the browser automatically attaching authentication cookies without the user’s awareness. With configurations such as SameSite=Lax or SameSite=Strict, the risk of unauthorized requests being executed is significantly reduced, even if users accidentally click on a malicious link.
Two-Factor Authentication (2FA)Link to heading
Two-factor authentication (2FA) does not directly prevent Cross-Site Request Forgery, but it plays a crucial role in limiting the potential damage if an attack occurs. When 2FA is enabled, sensitive actions or access to the administrative area require an additional verification step, such as a one-time password (OTP) or confirmation from a secondary device.
If an attacker attempts to exploit CSRF to carry out critical changes on an administrative account, this extra security layer creates a strong barrier, making full system compromise far more difficult.
>>> Learn more: Best practices to protect your WordPress login page
FirewallLink to heading
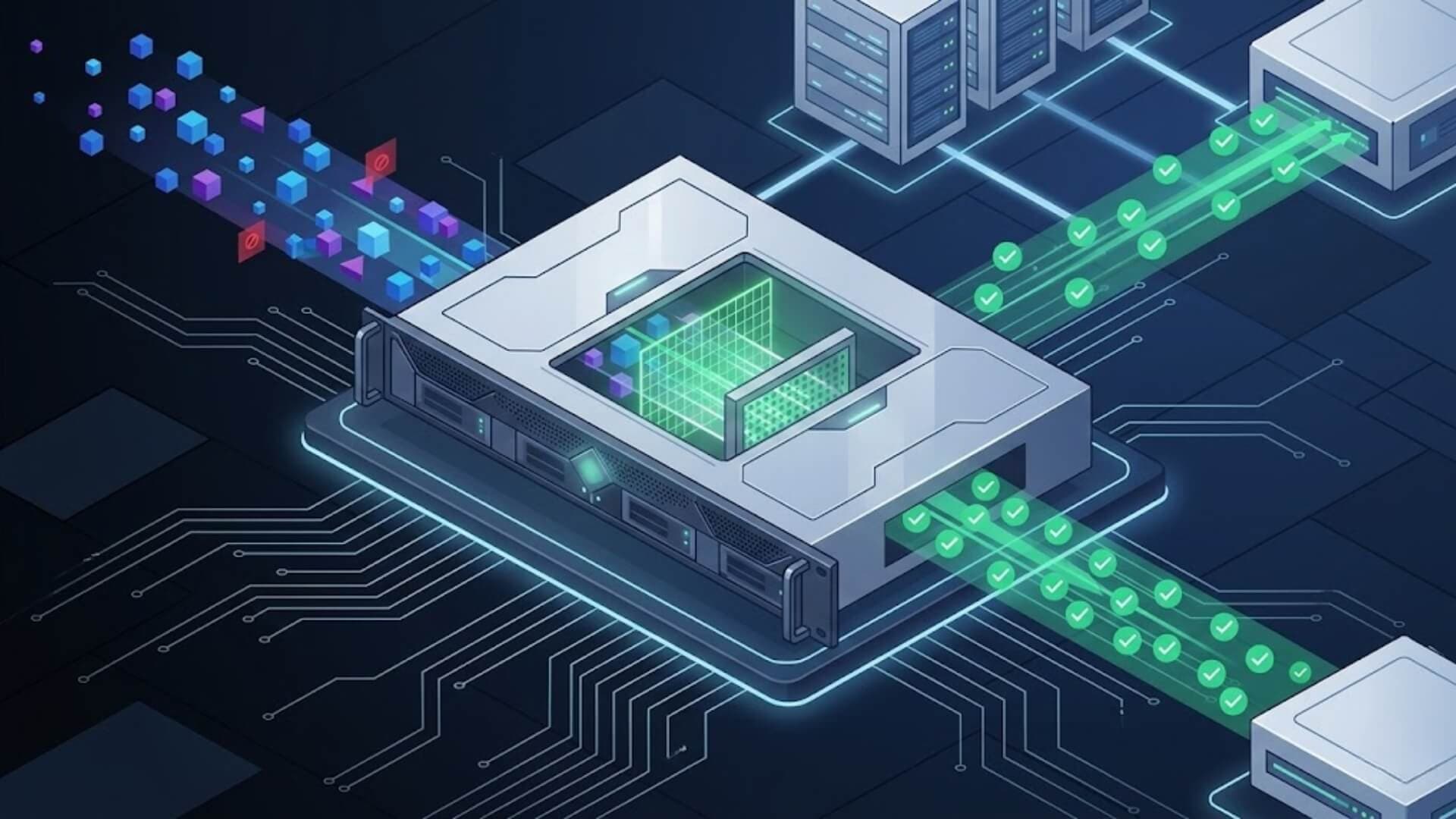
A firewall based on the “Block by Default” principle operates on a deny-first, allow-later model. Instead of trying to identify every specific attack pattern, the firewall automatically rejects any request that does not meet predefined security criteria. Only requests that are legitimate, behaviorally valid, and contextually appropriate are allowed to reach the system.
This type of firewall is particularly effective against Cross-Site Request Forgery, as malicious requests often exhibit abnormal characteristics in terms of origin, structure, or request flow. When properly implemented, a “Block by Default” firewall significantly reduces the attack surface and protects the website even from new CSRF variants that have not yet been documented.
>>> See more: Top 5 best WordPress firewalls in 2026

W7SFW – Proactive WordPress Firewall Solution
W7SFW is a WordPress Firewall designed with a proactive security mindset, helping websites block attacks at their root instead of merely reacting after incidents occur.
Operating under the Blacklist All → Default Rule + Whitelist model, and integrating Two-Factor Authentication (extension + password) along with sensitive file protection, W7SFW provides a robust layer of defense - even against threats that have never appeared before.
If you are managing a WordPress website and want to prevent risks such as CSRF attacks, administrative account takeover, or silent intrusions that leave no obvious traces, activating W7SFW today is a necessary step.
ConclusionLink to heading
Overall, Cross-Site Request Forgery is an attack technique that directly exploits user behavior and session-based authentication mechanisms, causing many administrators to discover the issue only after serious damage has occurred. To effectively reduce risk, websites must implement multiple layers of protection rather than relying on a single solution.
Proactively preventing CSRF from today is the most effective way to safeguard your system, protect user data, and preserve long-term brand value.